Among all international students that come into the United States, computer science ranks behind two other majors in terms of popularity.
Computer science is popular for quite a few reasons.
Reasons that typically include high starting wages, tremendous job security, and a broad range of job possibilities across many different industries. On the other hand, any international student that is considering taking up the study of computer science might have to ask themselves just what it is exactly.

Just what exactly is computer science?
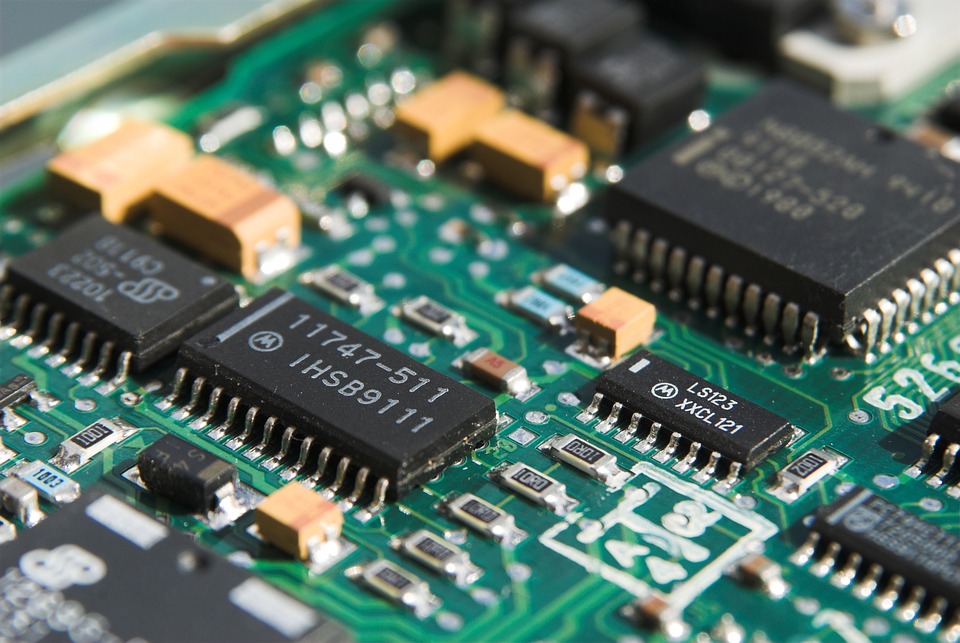
In general, the field of computer science means studying computer technology, in terms of both software and hardware. On the other hand, computer science is a very diverse field, and the necessary skills can be applied and are in fact in high demand in nearly every industry across the modern world, as it is very dependent on technology.
Given this, computer science as a larger field can be broken down into dozens of sub-disciplines, many of which are nowadays fully specialized disciplines.
Several dominant categories that fall under the computer science field include the core areas of software systems, hardware systems, scientific computing, and computer theory.
Students can pick classes and credits from these various sub-disciplines with different levels of specialization based on how they intend to apply their individual computer science degree.
The most stringent specializations typically happen in graduate-level education. However, it’s imperative that a student know just what computer science specifically is before they can know where their interests might lie in this expansive field of knowledge and skill, and that all adds up to knowing just how they should go about studying computer science.
The Many Disciplines of Computer Science
There are many different disciplines that fall within the purview of computer science. An international student needs to know how to go about studying computer science in order to learn their way around these many specialties and sub-groups. These are a few potential areas in which a student studying computer science might wind up specializing in:
- Applied Mathematics
- Artificial Intelligence
- Bioinformatics
- Computational Physics
- Computer Architecture Networks
- Computer Engineering
- Computer Game Development
- Computer Graphics
- Computer Programming
- Cryptography
- Data Management
- Design Databases
- Digital Image/ Sound
- iOS Development
- Memory Systems
- Microprogramming
- Mobile Development
- Networks and Administration
- Operating Systems
- Parallel Programming
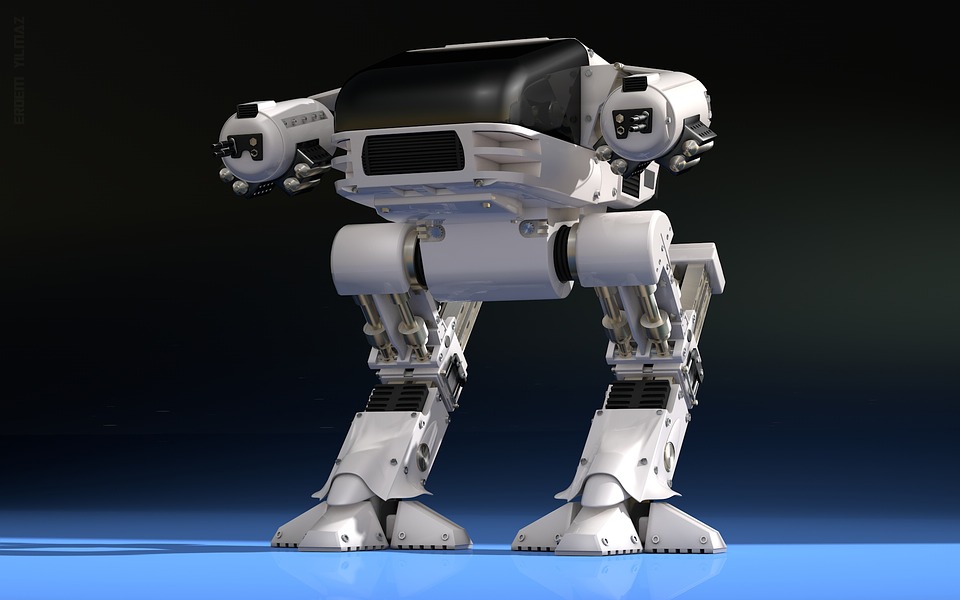
- Robotics
- Simulation and Modeling
- Software Development
- Software Systems
- Web Development
Given how many options are available, any international student that comes to the United States should have a very particular focus in mind in terms of their pursuit of a computer science degree, especially if they’re going to be seen as a serious job candidate in the future.
Knowing just how they should go about studying the field of computer science and then planning out the kind of degree they get will be contingent upon a student understanding the broader discipline and then deciding for themselves if that degree is the right way to approach a career path.
As such, it’s crucial to pick out a particular computer science degree that lets you go after the kind of career that you would like to have.
Even with the apparently countless ways an international student could study computer science while inside the United States, they still have to ask the central question of what computer science is before they can start their hopefully successful education and then career.
However, there are numerous resources, many of them free, available to those who are studying the field of computer science.
For example, one great resource international students can use while studying computer sciences at an educational institution within the United States are websites of specific institutions, many of them, but not all educational. Such websites have lots of great content about the computer science curriculum available at that institution, including specialties, but they might also have resources that cater specifically to international students. This could include things like ongoing research, opportunities for internships and scholarships, and program course credit breakdowns.
The Study Computer Science guide is also a powerful resource that international students might use. This guide has quite a bit of information involving topics from advice about internships and careers to where a person should study computer science.